
Hackers tipped off Dutch telco Odido about its own data breach
Telecom provider Odido was unaware for two days that the hack in early February had resulted in a massive dat...

Telecom provider Odido was unaware for two days that the hack in early February had resulted in a massive dat...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Foxconn has confirmed a cyberattack on its North American factories. The Nitrogen ransomware group posted the...

Telecom provider Odido was unaware for two days that the hack in early February had resulted in a massive dat...

During May’s Patch Tuesday, Microsoft released fixes for 137 vulnerabilities in Windows, Azure, Dynamics 36...

LLMs are proving increasingly useful for security research. Cisco aims to standardize and streamline the proc...

Update (Erik van Klinken, May 12, 12:10 PM): Instructure, the maker of the Canvas learning platform, has reac...
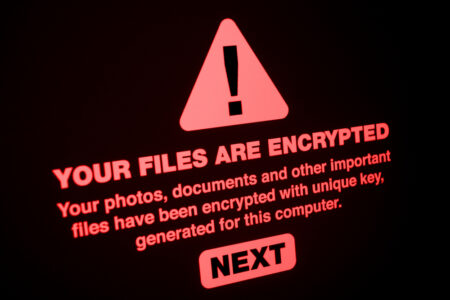
A surprisingly positive development: ransomware is on the decline. The share of organizations affected by the...

Google says it likely prevented a cyberattack in which hackers used AI to develop a zero-day vulnerability. A...


A tampered version of the Checkmarx Jenkins AST plugin has appeared in the Jenkins Marketplace. The attack ha...

Ivanti has addressed five vulnerabilities in Endpoint Manager Mobile (EPMM). One of them, CVE-2026-6973, is b...