Editor picks
OpenAI makes official move for an IPO
OpenAI has filed a confidential S-1 document with the U.S. Securities...
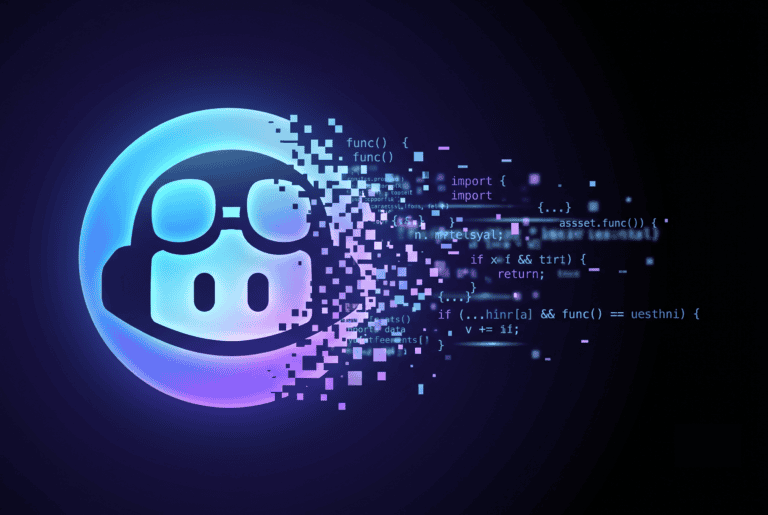
ChatGPT easily bypasses its own guardrails; all LLMs are inherently unsafe
ChatGPT does whatever the hacker wants after manipulation
Zscaler optimizes Zero Trust for agentic AI security
Zscaler announces a series of security features for agentic AI. The c...
QuiX Quantum drives control tools for Photonic Quantum era
Netherlands-headquartered photonic quantum computing hardware company...
"*" indicates required fields
Story timeline
Taking the right lessons from AI success stories
While a lot of the current narratives around AI focus on stalled initiatives or pilots that never transl...

Microsoft resumes automatic rollout of Copilot on PCs
Microsoft has resumed the automatic installation of the Microsoft 365 Copilot app on business Windows systems...

Microsoft is exploring the use of Claude Fable to implement new retention periods
For now, Microsoft is holding back Anthropic’s latest AI technology for internal use. The company is invest...
Claude Fable 5 is Mythos for the masses
After months of speculation, Mythos Preview has finally been turned into a properly released LLM. It takes th...

ShinyHunters targets Oracle PeopleSoft
A large-scale attack campaign is currently targeting organizations that use Oracle PeopleSoft. The ShinyHunte...
AWS Graviton5 available via M9g and M9gd instances
Amazon Web Services has made the M9g and M9gd instances, based on the Graviton5 processor, generally availabl...
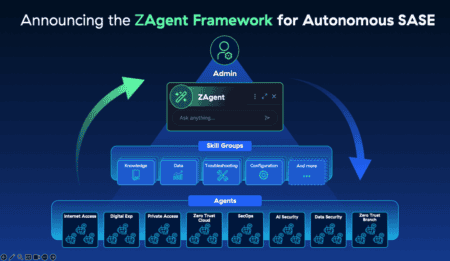
Zscaler launches ZAgent Framework for agentic AI administration
Zscaler announces a significant expansion of its Zero Trust SASE platform. The company is introducing the ZAg...

Zscaler optimizes Zero Trust for agentic AI security
Zscaler announces a series of security features for agentic AI. The company is expanding its Zero Trust Excha...

TSMC sales jump 30 percent as AI chip demand stays strong
TSMC posted a 30 percent rise in May revenue to NT$416.98 billion (roughly 11 billion euros), driven by susta...

ServiceNow patches vulnerability after unauthorized access
ServiceNow has notified customers of a security incident in which unauthorized parties accessed data from cus...

Supermicro to invest $7 billion in expanding AI server production
Supermicro aims to raise $7 billion through a major funding round to keep pace with the growing demand for AI...

AWS launches FinOps Agent for cost management
AWS has launched AWS FinOps Agent in public preview. The agent-based AI solution automatically investigates c...

OpenAI makes official move for an IPO
OpenAI has filed a confidential S-1 document with the U.S. Securities and Exchange Commission (SEC). With thi...

SAP patches vulnerabilities in NetWeaver and Commerce Cloud
In its monthly security update, SAP addressed fifteen vulnerabilities, including four critical security flaws...

Datadog update tackles AI and security complexity
Datadog has unveiled more than a hundred new features. The announcements focus on autonomous operations, AI a...

Nextcloud Hub 26 Spring is ‘designed for the future’
Nextcloud is now ten years old. The anniversary release, Nextcloud Hub 26 Spring, introduces features that de...

DataCore guarantees prices and delivery of enterprise storage
DataCore is introducing the “Buy with Confidence” program to protect enterprise storage customers from pr...
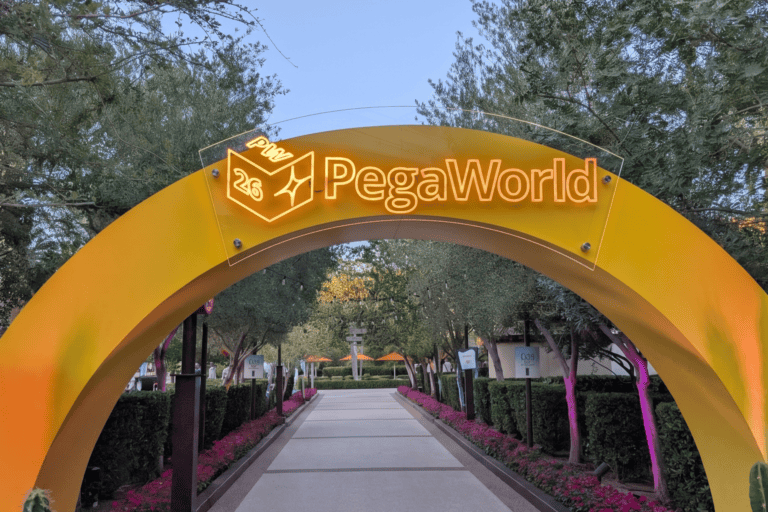
From token maxxing to tokenomics: Pega keeps AI real and pragmatic
Blueprint AI integrates with Infinity to form Infinity Studio
Broadcom bolsters Spring security with largest update ever
Broadcom announces the largest series of Spring security updates in the framework’s 23-year history. The Ta...
Neurometric AI & LumaDock aim to slash OpenClaw inference costs
Neurometric AI is the inference orchestration company behind ClawPack, an advanced simulation mathematics tec...
The AI trailblazer GitHub Copilot is running out of road
It’s easy to forget that GitHub Copilot appeared on the scene a year and a half before ChatGPT. The AI assi...

Microsoft investigates malware in GitHub repos
Microsoft has temporarily taken dozens of open-source projects on GitHub offline due to an investigation into...

Databricks valued at up to $175 billion in new funding round
Databricks is in talks regarding a new funding round that would value the company at between $165 billion and...

KPN’s acquisition of Delta networks prohibited
The Dutch Authority for Consumers and Markets (ACM) has prohibited the proposed acquisition of part of Delta ...

Check Point warns of critical VPN authentication vulnerability
Check Point Research has discovered an actively exploited authentication vulnerability in Remote Access VPN a...

ConnectWise launches platform for Predictive IT
ConnectWise introduces the ConnectWise Platform for managed service providers. PSA, RMM, cybersecurity, autom...

Alation serves up Semantic Model Mastering, it’s MDM for the semantic layer
Alation is the company we know for its data intelligence platform, designed to centralise data cataloguing, g...

NTT DATA and Google Cloud expand collaboration on agentic AI
NTT DATA and Google Cloud are expanding their partnership to help companies deploy agentic AI at scale. Th...

AI actually boosts demand for tech talent, says Linux Foundation
Artificial intelligence is not yet leading to a contraction of the IT labor market. On the contrary: organiza...
SK Hynix is in Nvidia’s good graces for AI memory
Nvidia and SK Hynix are further expanding their partnership with a multi-year agreement to develop new genera...

Linux kernel 7.1 is almost ready
The development of Linux 7.1 is in its final stages. Linus Torvalds (photo) has released release candidate 7 ...
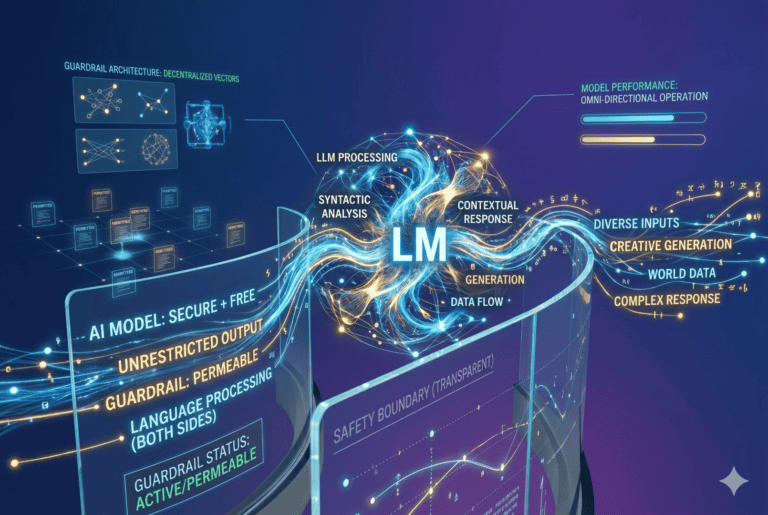
ChatGPT easily bypasses its own guardrails; all LLMs are inherently unsafe
ChatGPT does whatever the hacker wants after manipulation

Google to pay SpaceX $920M every month for xAI compute
Google has signed a deal to pay SpaceX $920 million per month for AI compute capacity housed in xAI's data ce...

Klarrio: Architecture is either the biggest bottleneck or the biggest accelerator
Klarrio has published a white paper on the role of architecture in software projects. The company argues that...

ASML supports EU cloud plans but warns against bureaucracy
ASML CEO Christophe Fouquet welcomes the EU’s sovereignty package as an important step forward. The company...

AMD gains ground in servers thanks to AI boom, Intel remains market leader
AMD has once again strengthened its position in the server market. According to new figures from market resea...

Cloudflare acquires Vite developer VoidZero
Cloudflare is acquiring VoidZero, the company behind popular JavaScript tools such as Vite, Vitest, Rolldown,...
Anthropic’s AI fearmongering isn’t what it appears to be
"Recursive AI" remains purely speculative

Nvidia selects top three vendors for critical AI memory
Nvidia has selected the three largest memory chip manufacturers to supply HBM4 memory for its next-generation...

Synology updates at Computex focus on data control
Call it sovereignty, digital autonomy, or resilience—Synology is emphasizing a solution that drives it. At ...
Infoblox IQ brings agentic AI to network and security management
Infoblox has announced Infoblox IQ, an agentic operations layer built on top of the existing DDI platform. Th...

VS Code now maintains AI context across devices
Microsoft announced a new version of Visual Studio Code during its Build 2026 developer conference. Version 1...

QuiX Quantum drives control tools for Photonic Quantum era
Netherlands-headquartered photonic quantum computing hardware company QuiX Quantum has detailed its new Feed-...

WP Engine expands Global Edge Security with bot management
WP Engine is adding customizable bot management features to Global Edge Security (GES), powered by Cloudflare...
TSMC expects AI chip shortage to persist for years
Global demand for AI chips continues to far exceed production capacity. That’s according to TSMC CEO C.C. W...

Broadcom under pressure after revenue disappointment
Broadcom disappointed investors with quarterly results that fell just short of expectations. Although the chi...

Quobly raises €115M to bring silicon qubits to market
French quantum computing company Quobly has closed a 115 million euro Series A financing round, led by Bpifra...

EU data center sustainability label delayed over nuclear controversy
The European Commission has postponed a planned sustainability label for data centers amid a dispute over nuc...

GitLab cuts 14 percent of staff to fund agentic AI push
GitLab is laying off roughly 14 percent of its workforce, about 350 people, and withdrawing from 22 countries...
