
MITRE CVE database saved after last minute reversal
The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...

The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.
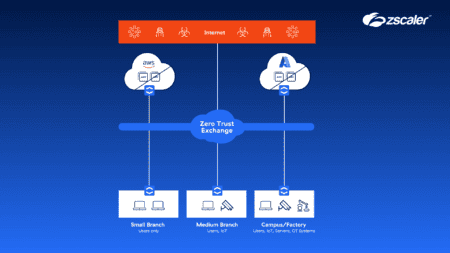
With its new Zero Trust Segmentation solution, Zscaler aims to help companies securely connect users, devices...


Microsoft's Patch Tuesday update for this month includes as many as 91 different fixes for security vulnerabi...

With Falco Feeds, Sysdig provides customers with the most up-to-date information on cyber threats. Cloud thre...
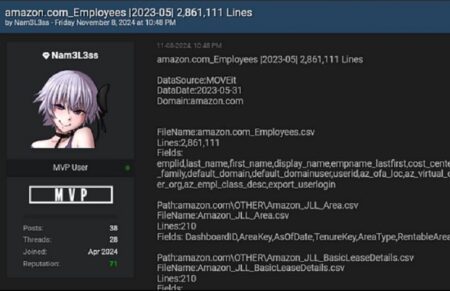
Amazon confirms a data breach in which employees' personal data was leaked. This data breach is part of a lar...

With Manifest V3, Google wants to make Chromium browsers more secure. That's a relative term, because V3-base...

Hackers are increasingly using files for Microsoft Visio to lure unsuspecting computer users to phishing site...

Hackers are attempting to spread the malicious software framework Winos4.0 to Windows endpoints via game-rela...


Update 8/11: Nokia ends the first days of the investigation with positive news. According to the company, the...