
Security

Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.
Timeline
Windows IoT Core vulnerable to hackers
A security researcher discovered a leak in Windows IoT Core that a hacker can use to take control of a device....

“Cryptojacking increased by 450 percent in 2018
Cryptojacking attacks, in which hackers steal processor power from victims to generate cryptic currency, incre...

Microsoft: Hackers steel large sums of financial institutions
According to Microsoft, hackers, sponsored by governments, were able to raise large sums of money last year by...

Microsoft wants to increase its presence on the cyber security market with Azure Sentinel
Microsoft has increased its presence in the cyber security market with the introduction of Azure Sentinel. Tha...

Zero-day in Chrome is used to collect information via PDFs
Security company EdgeSpot has discovered PDF documents that take advantage of a zero-day leak in Google Chrome...
Vulnerability in super-micro-hardware can bring backdoor to IBM cloud server
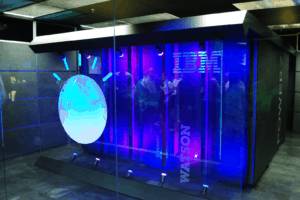
A five year old vulnerability in a widely used administrative tool for servers used for sensitive and mission-...

Intel brings SGX to data centers with new hardware
Intel launches the SGX map. That piece of hardware that has slightly older hardware that is compatible with so...

2.4 million sensitive user data leaked Dow Jones
Dow Jones has leaked 2.4 million user data through an incorrectly configured Amazon Web Services (AWS) server....

Hackers spread malware through fake accounts on LinkedIn
Security researchers have discovered that hackers are increasingly focusing on LinkedIn users. They offer them...

Cloudborne vulnerability exposes cloud servers to hackers
A new vulnerability has been found that may enable hackers to capture data that companies store in the cloud. ...