
MITRE CVE database saved after last minute reversal
The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...

The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.

Earlier this week, press agency Bloomberg stated that China had secretly placed small chips on Supermicro's mo...

Amazon and Apple are said to be targets of Chinese espionage. It is said that chips have been placed on the mo...

Palo Alto Networks announces that it has reached an acquisition agreement with RedLock. The cloud security spe...
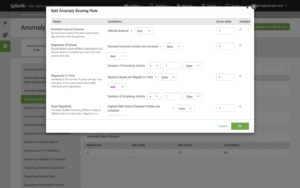
Splunk has announced new innovations to its security portfolio to help security teams detect and investigate c...

More than 12 million email archive files are accessible due to misconfigured rsync, FTP, SMB, S3 bucket and NA...

The Military Intelligence and Security Service (MIVD) has foiled a hacking operation by the Russian military s...
Last Wednesday, millions of Americans received something similar to a text message from President Donald Trump...

The British National Cyber Security Centre reports after investigation that the Russian military secret servic...

The developers of Ubuntu and Debian receive a warning from Googles Project Zero. Project Zero researcher Jann ...

Developers of extensions for Google Chrome are the newest target of hackers. It seems that hackers are trying ...