
MITRE CVE database saved after last minute reversal
The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...

The US government is extending funding for the Common Vulnerabilities and Exposures (CVE) database by eleven ...
Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.
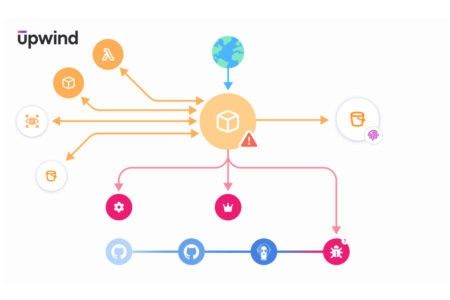
Upwind adds real-time API security to the Cloud Application Detection and Response (CADR) framework. This sho...

Several major Australian pension funds have been targeted in a coordinated cyber attack that potentially comp...

Oracle has informed customers about a new hack. Login credentials have been stolen. The FBI and CrowdStrike a...

Check Point has reassured its customers after a hacker claimed to have obtained some of the company's valuabl...

A self-proclaimed data enthusiast calling themselves 'ThinkingOne' has made a huge database containing 201 mi...



VMware Workstation users report that the software's automatic update functionality no longer works. This is a...

Cloudsmith is introducing new security functions for enterprise container management. They will be welcomed b...

A new cyber attack uses a driver called ABYSSWORKER to disable security software. The driver is part of a fin...