
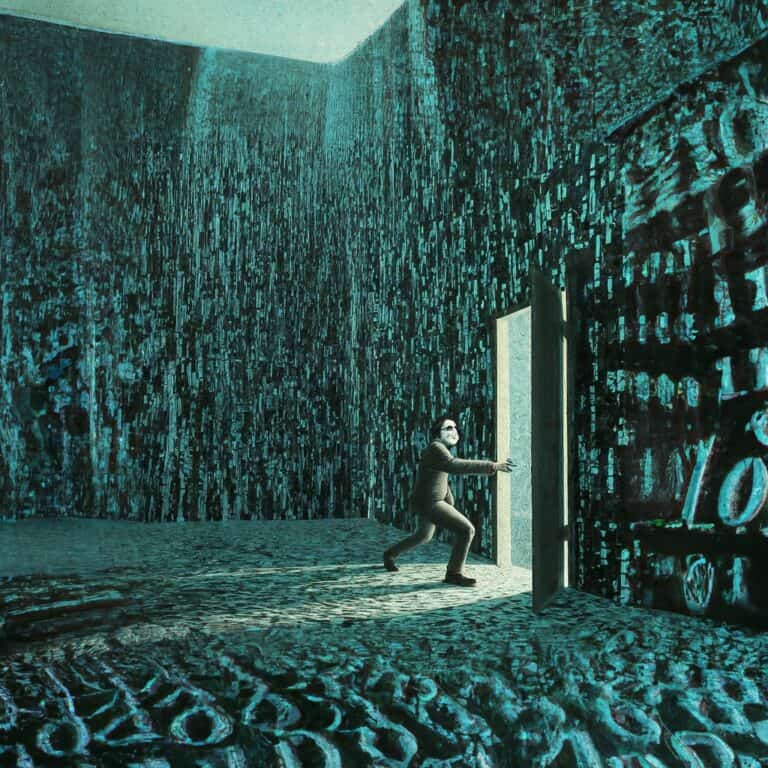
Security

Cybersecurity has been a challenge from the beginning of IT and it will be until the end. It all started with endpoint and network security, but today we are also dealing with cloud security and training our employees to incorporate good security practices. All these new technologies that help us innovate also help cybercriminals and state-sponsored hackers get new tools that they can use to access our systems and, in the worst cases, gain access to our most valuable data and trade secrets. Moreover, with new legislation such as GDPR, you have to make sure everything is secure or you will not only lose your reputation, but you could also be fined by the government. In short, protecting IT environments is more important than ever.
Timeline

Internal IT environment TeamViewer hacked
TeamViewer's internal IT environment was recently the target of a cyber attack. The hackers penetrated the in...

Cloudflare redirects all Pollyfill.io links on its customers’ sites to secure mirror
Cloudflare is replacing all references to the Polyfill.io domain in a highly unusual move. The open-source Ja...

CyberArk extends PAM solution to machine identities
Like a spider builds a web, CyberArk is continually increasing the number of profiles for which it has securi...

There is no OT apocalypse, but OT security deserves more attention
Real ransomware attacks on OT are rare

1,800 networks at risk from new MOVEit vulnerability
MOVEit software contains a dangerous vulnerability. At least 1,800 networks are running these versions of the...

Ransomware attacks are increasingly used as cover for espionage activities
Cyber-espionage groups are increasingly using ransomware attacks to make their attempts at sabotage and data ...

Netherlands gets six Russian hackers put on European sanctions list
The Netherlands has arranged for the European Council of Foreign Ministers to put six Russian hackers on the ...
Makers of infamous xz backdoor cleverly managed to cover their tracks, analysis shows
The backdoor in the xz compression tool for Linux that came to light earlier this year used several sophistic...

‘Substantial risk of malicious extensions in Chrome Web Store’
According to security researchers, the risk of users downloading a malicious browser extension from the Chrom...

NinjaOne steps into Mobile Device Management
The NinjaOne platform goes beyond Unified Endpoint Management by fully supporting end-user, infrastructure an...